The JN0-348 dumps are very important when preparing for the Juniper JNCIS-ENT certification JN0-348 exam, and it’s great JN0-348 study material. We have updated the latest JN0-348 dumps to help you learn.
Because the JN0-348 dumps provide you with a test room scenario, such as what questions and answers will be included in the exam. If you have JN0-348 dumps learning materials ready, then Pass4itSure is your path to success. Go to the Pass4itSure JN0-348 dumps page to download it: https://www.pass4itsure.com/jn0-348.html, good learning materials ensure success.
Online support for JN0-348 free dumps exam study materials: https://drive.google.com/file/d/1ggfRgd4v0MCgO86yGx8laHGrk5trPOs8/view?usp=sharing
Which ones are? What is the important knowledge of the Juniper JN0-348 exam?
Full exam name: Enterprise Routing and Switching, Specialist (JNCIS-ENT)
Abbreviation: JN0-348
For the crowd: Designed by experienced network professionals with knowledge of beginner to intermediate Junos routing and switching implementations
Certification Direction:
JNCIA-Junos
JNCIS-ENT
JNCIP-ENT
JNCIE-ENT
Recommended Resources:
Junos Intermediate Routing (JIR)
Junos Enterprise Switching (JEX)
Industry/product knowledge
Juniper TechLibrary
Juniper Learning Portal
Exam Language: English
Exam duration: 90 minutes
Exam Type: 65 multiple-choice questions
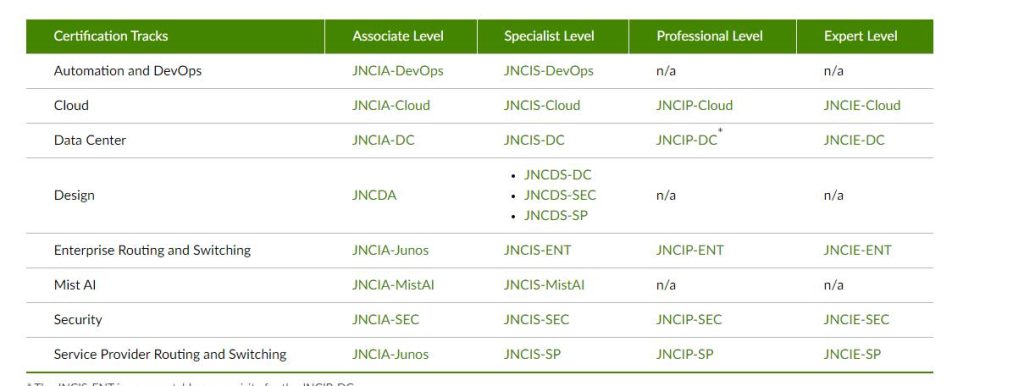
Juniper certification general outline
As shown in the figure below, you can understand the certification direction of Juniper and the corresponding certificate
What is the key to success in the Enterprise Routing and Switching, Specialist JN0-348 exam?
If you have great Juniper JN0-348 dumps learning materials in place, it’s your path to success. Here, the Pass4itSure JN0-348 dumps are pushed.
Free JN0-348 Questions and Answers
QUESTION # 1
Click the Exhibit button.
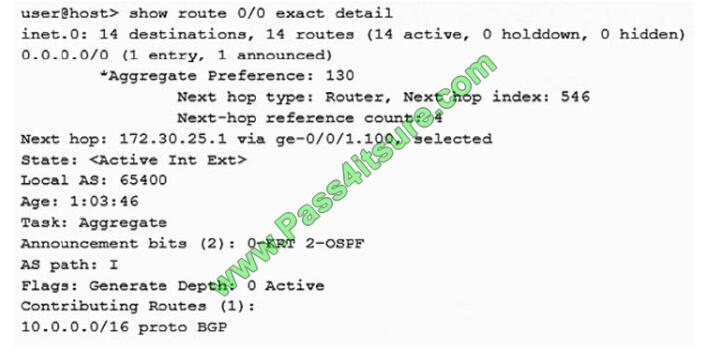
Referring to the output shown in the exhibit, which two statements are true?
A. The route is active
B. The route is not active
C. The route is a generated route
D. The route is an aggregate route
Correct Answer: AC
QUESTION # 2
What are two advantages of a point-to-point OSPF adjacency? (Choose two.)
A. Only a DR is elected.
B. No type 1 LSAs are generated.
C. No type 2 LSAs are generated.
D. There is the quicker neighbor establishment.
Correct Answer: CD
QUESTION # 3
Which statement is correct about IS-IS link-state PDUs?
A. They are used to maintain link-state database synchronization.
B. They are used to establish adjacencies.
C. They are used to build the link-state database.
D. They are used to determine whether the neighbors are Level 1 or Level 2.
Correct Answer: C
QUESTION # 4
What are two benefits of 802.3ad link aggregation? (Choose two.)
A. It increases bandwidth.
B. It ensures symmetrical paths.
C. It simplifies interface configuration.
D. It creates physical layer redundancy.
Correct Answer: AD
QUESTION # 5
You want to configure Layer 2 services over an IP-based tunneling mechanism between two sites.
Which configuration statement is required to accomplish this task?
A. set interfaces gr-0/0/0.0 family bridge
B. set interfaces IP-0/0/0.0 encapsulation VLAN-bridge
C. set interfaces gr-0/0/0.0 encapsulation VLAN-bridge
D. set interfaces IP-0/0/0.0 family bridge
Correct Answer: A
QUESTION # 6
What are two methods for reducing the size of an OSPF link-state database? (Choose two.)
A. Use unique router IDs where possible.
B. Use identical link metrics where possible.
C. Use point-to-point interface types where possible.
D. Use stub areas where possible.
Correct Answer: CD
QUESTION # 7
Your network is configured with dynamic ARP inspection (DAI) using the default parameters for all the DHCP and ARP-related configurations. You just added a new device connected to a trunk port and configured it to obtain an IP address
using DHCP. Which two statements are correct in this scenario? (Choose two.)
A. The DHCP server assigns the IP addressing information to the new device.
B. DAI validates the ARP packets for the new device against the DHCP snooping database.
C. The ARP request and response packets for the new device will bypass DAI.
D. DHCP snooping adds the DHCP assigned IP address for the new device to its database.
Correct Answer: AB
QUESTION # 8
Which two statements are true about high availability on Junos devices? (Choose two.)
A. BFD is faster at detecting failures than default GRE or OSPF timers.
B. BFD is slower at detecting failures than default GRE or OSPF timers.
C. NSR is dependent on helper routers to assist the routing platform in restoring routing protocol information.
D. NSR is independent of helper routers to assist the routing platform in restoring routing protocol information.
Correct Answer: AD
QUESTION # 9
When electing a DIS in an IS-IS network, what is used to break a priority tie?
A. highest MAC address
B. highest router ID
C. lowest MAC address
D. lowest router ID
Correct Answer: A
QUESTION # 10
Click the Exhibit button.
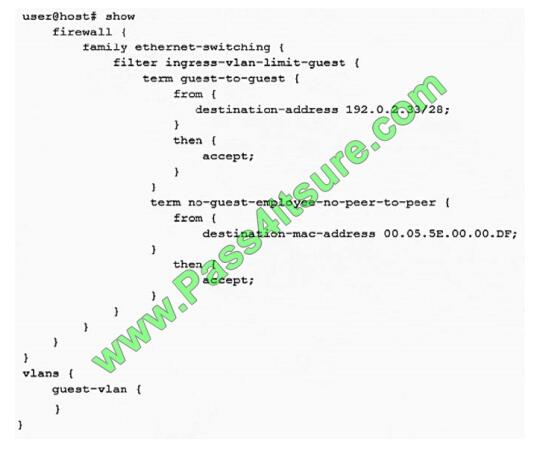
A recent security audit indicates that peer-to-peer applications are allowed on the guest VLAN and employees may have been using the guest VLAN for this purpose. You deploy the configuration shown in the exhibit, but it does not stop the peer-to-peer traffic. In this scenario, what must you do to implement the security policy?
A. Implement 802.1X on the guest VLAN
B. Attach the filter to the VLAN
C. Deploy storm control to block unknown unicast traffic
D. Use persistent MAC learning
Correct Answer: B
QUESTION # 11
Which statement is true about IP-IP tunnels?
A. The time-to-live value of the original packet is decremented.
B. IP-IP tunnels are protocol agnostic.
C. The packet is encapsulated unchanged before entering the tunnel.
D. The packet header is replaced before entering the tunnel.
Correct Answer: B
QUESTION # 12
Which two elements are used to create the STP bridge ID? (Choose two.)
A. the root port number
B. the bridge priority value
C. the system MAC address
D. the port cost
Correct Answer: BC
QUESTION # 13
Which two statements are correct regarding the root bridge election process when using STP? (Choose two.)
A. A lower system MAC address is preferred.
B. A higher bridge priority is preferred.
C. A lower bridge priority is preferred.
D. A higher system MAC address is preferred.
Correct Answer: AC
View more JN0-348 questions, here